The Small
Business
Cyber Security Guy
⭐100K+ Monthly Downloads
⭐Top 20 Apple Management
⭐100K+ Monthly Downloads ⭐Top 20 Apple Management
Welcome to the blog and podcast, where we share brutally honest views, sharp opinions, and lived experience from four decades in the technology trenches. Whether you're here to read or tune in, expect no corporate fluff and no pulled punches.
Everything here is personal. These are my and the team’s thoughts, opinions forged in the heat of battle! And not those of our employers, clients, or any other professional with whom we are associated.
If you’re offended, take it up with us, not them.
What you’ll get here (and on the podcast):
Straight-talking advice for small businesses that want to stay secure
Honest takes on cybersecurity trends, IT malpractice, and vendor nonsense
The occasional rant — and yes, the occasional expletive
War stories from the frontlines (names changed to protect the spectacularly guilty)
I've been doing this for over 40 years. I’ve seen genius, idiocy, and everything in between. Some of it makes headlines, and most of it should.
This blog and the podcast are where we break it all down.
Grab a coffee and pull up a chair, you need to see this!
UK SMBs Left in the Crosshairs
If you run a small or medium-sized business in the UK, the government just sent you a message: you are on your own. The November 2025 Cyber Security and Resilience Bill protects hospitals and power grids. It does not protect you.
Of 5.5 million UK SMBs, exactly zero gained new cybersecurity protection.
This was deliberate policy.
Meanwhile, 43% of UK businesses experienced breaches last year, costing an average £3,550 per incident. Germany took a different approach—and it works.
This article gives you the statistics, the proof, and the action plan you can start Monday morning.
Directors Should Face Criminal Liability for Cyber Security Negligence. Here's Why.
Directors should face criminal prosecution for cyber security negligence. The HSE precedent proves personal criminal liability transforms director behaviour. Before HSE had teeth, workplace deaths were common. After directors faced imprisonment, safety transformed. Civil liability isn't working for cyber security: 73% of businesses lack board responsibility despite 43% breach rates and 28% closure risk. Friday's case study showed £3.337 million loss preventable with £90 investment. Proposed: Criminal prosecution when directors fail documented risk assessment, basic controls, board-level responsibility, systematic review, causing serious harm. Test: reasonable care. Penalty: up to two years imprisonment. Business lobbying will kill this. Meanwhile preventable disasters continue.
When Boards Ignore Risk Registers: The £2.4 Million Manufacturing Disaster That Nobody Learned From
March 2024: UK manufacturing company with £18 million turnover lost £2.4 million to business email compromise. Finance director phished, email credentials stolen (no MFA), attacker monitored for two weeks, sent fraudulent payment instruction from compromised account, major client processed payment overseas. Total immediate costs £3.337 million. Company survived through private equity investment that diluted family ownership from 100% to 23%. Managing director resigned. Eight redundancies. What would have prevented it: two-hour risk register workshop identifying the CRITICAL risk. Additional controls needed: MFA on email (£0), FIDO2 keys (£90), payment verification procedures (policy change). Total prevention cost: £90 plus seven hours implementation.
Your First Cyber Risk Register: 2-Hour Implementation Guide with Template
Create your first cyber risk register in 2 hours. No consultant needed.
Step 1: Identify five specific risks (phishing, ransomware, insider threats are mandatory for all UK SMEs).
Step 2: Assess likelihood using real government statistics (85% phishing, 43% breach rate).
Step 3: Document impact including business closure potential (28% of SMEs).
Step 4: List current controls with verification dates. Step 5: Calculate residual risk scores.
Step 6: Specify additional controls with costs.
Step 7: Assign board-level owners.
Step 8: Create quarterly review schedule.
Total time: 2 hours creation plus 30 minutes quarterly.
Eight hours annually to manage business-ending risks. Template included.
The Psychology of Risk Denial: Why Smart People Convince Themselves They're Too Small to Matter
Why do intelligent board members hear "43% of UK businesses got breached" and think "that won't happen to us"? It's not stupidity; it's psychology. Optimism bias makes us believe bad things happen to others. Present bias makes tomorrow's disaster less urgent than today's deadline.
Availability heuristic makes personal experience trump statistics. Illusion of control makes certificates feel like protection.
Normalcy bias treats "it hasn't happened yet" as evidence. Dunning-Kruger creates confident ignorance. Graham Falkner demonstrated all these biases on Episode 31. Understanding this psychology changes how you present cyber risk to boards.
Facts alone don't work. Systematic bias dismantling does.
How to Build a Cyber Risk Register That Actually Works: The Technical Reality Behind Board Governance
Most cyber risk registers are useless compliance documents.
They contain vague descriptions, unverifiable controls, and no honest assessment of likelihood or impact.
A working risk register has exactly seven columns: specific risk scenarios, likelihood based on real UK statistics, quantified impacts including business closure potential, verifiable current controls, residual risk ratings, costed additional controls, and named board-level owners.
Every UK SME must address five mandatory risks: phishing (85% of breaches), ransomware, supply chain compromise, insider threats, and cloud misconfiguration.
Ten critical technical controls cover 90% of actual threats. Implementation costs £150-300 per user annually. One prevented £3,398 breach pays for years of protection.
iOS 26.2: Apple Confirms Active iPhone Attacks Against Business Targets
Apple released iOS 26.2 on 12 December 2025 patching two WebKit zero-day vulnerabilities that were actively exploited before patches existed. Google's Threat Analysis Group discovered CVE-2025-43529 and CVE-2025-14174 being used in sophisticated attacks against targeted individuals. These vulnerabilities allow arbitrary code execution through malicious websites with no user interaction required.
The update patches over 20 vulnerabilities total, including a kernel bug allowing root access and an App Store flaw exposing payment tokens. For business owners, running unpatched devices with known exploits fails UK GDPR requirements and creates director liability. Update every business iPhone immediately.
The Risk Register Argument - When Your Co-Host Says You're Wrong About Governance
Graham Falkner told me before recording that small businesses don't need formal cyber risk registers. By the end of Episode 31, he'd completely changed his mind.
UK government data shows only 27% of businesses have board-level cyber security responsibility, down from 38% in 2021. Meanwhile, 43% got breached and 28% of SMEs say a single attack could put them out of business. The evidence is overwhelming. Risk registers aren't bureaucracy - they're systematic thinking applied to survival.
This episode documents Graham's complete conversion from skeptic to believer, and challenges every UK board to create a risk register this week.
Opinion: IoT Security Is Security Theatre Until We Make Default Passwords Illegal
Right, I'm done being diplomatic about this. After 40 years watching the same preventable disasters repeat themselves with different technology, I'm calling it: selling network-connected devices with default administrative credentials should be illegal in the UK. Not "discouraged."
Not "recommended against." Illegal. With criminal penalties for manufacturers and civil liability for distributors. Pull up a chair. This intervention has been brewing for three decades. The free market has had 30 years to fix IoT security. Manufacturers are still shipping printers with admin/admin. I want company directors facing personal criminal liability. Think I'm wrong? Read this. Then tell me why in the comments.
When the Password Manager Fails at Passwords: The £1.2 Million LastPass Lesson
The ICO just fined LastPass £1,228,283 for security failures. Yes, a password manager company, fined for password security failures. The irony would be funny if 1.6 million UK customers hadn't had their data compromised. LastPass allowed senior employees to access corporate vaults from personal devices and let them link business and personal accounts with one master password. When an attacker exploited vulnerable Plex software on an engineer's home computer, they grabbed the keys to everything. If you're running a UK small business, this £1.2 million lesson teaches you exactly what not to do.
The 5-Step IoT Device Audit: Find and Secure Every Forgotten Computer on Your Network (Copy)
A 30-person marketing agency in Manchester did everything right. £15,000 invested in proper security: new firewalls, enterprise endpoint protection, hardware authentication keys for every staff member, and even an external security audit that came back clean.
They were feeling quite good about themselves. Two months later?
Someone had been accessing their client files for weeks through their HP printer that still used admin/admin as credentials.
Total costs: £43,400 direct expenses, three lost clients, five renegotiated contracts, and ongoing competitive damage.
This is the complete story of how a £300 printer defeated a £15,000 security investment.
Real timeline. Real costs. Real lessons you need before this happens to you.
The 5-Step IoT Device Audit: Find and Secure Every Forgotten Computer on Your Network
Practical Value: After Monday's podcast about the marketing agency breach through an unsecured printer, the most common question we've received is: "How do I actually do this audit myself?" Fair question.
Telling business owners they have a problem is easy. Providing practical steps to fix it is harder. This guide walks you through conducting a comprehensive IoT device audit using free tools. Time investment: 4-6 hours for initial audit.
Cost: Free to £200 for network scanning tools.
Difficulty: Intermediate. Can be done by office managers with IT support.
Discover every forgotten device before attackers do.
Start this weekend.
Prevent your £43,000 breach.
Three Zero Days And A Christmas Timebomb: December Patch Tuesday Will Hurt If You Ignore It
December 2025 Patch Tuesday is supposed to be the quiet cruise into Christmas, right? Instead we got fifty seven vulnerabilities, three zero days and one actively exploited Windows privilege escalation that hits almost every supported build.
Add in one hundred and thirty nine Adobe fixes and an awkward five week gap until the next Patch Tuesday in January and you have a perfect festive storm.
Are you really happy to leave servers and laptops unpatched while everyone is on holiday, or do you want to start 2026 without starring in a breach headline? What does your patch plan look like this week?
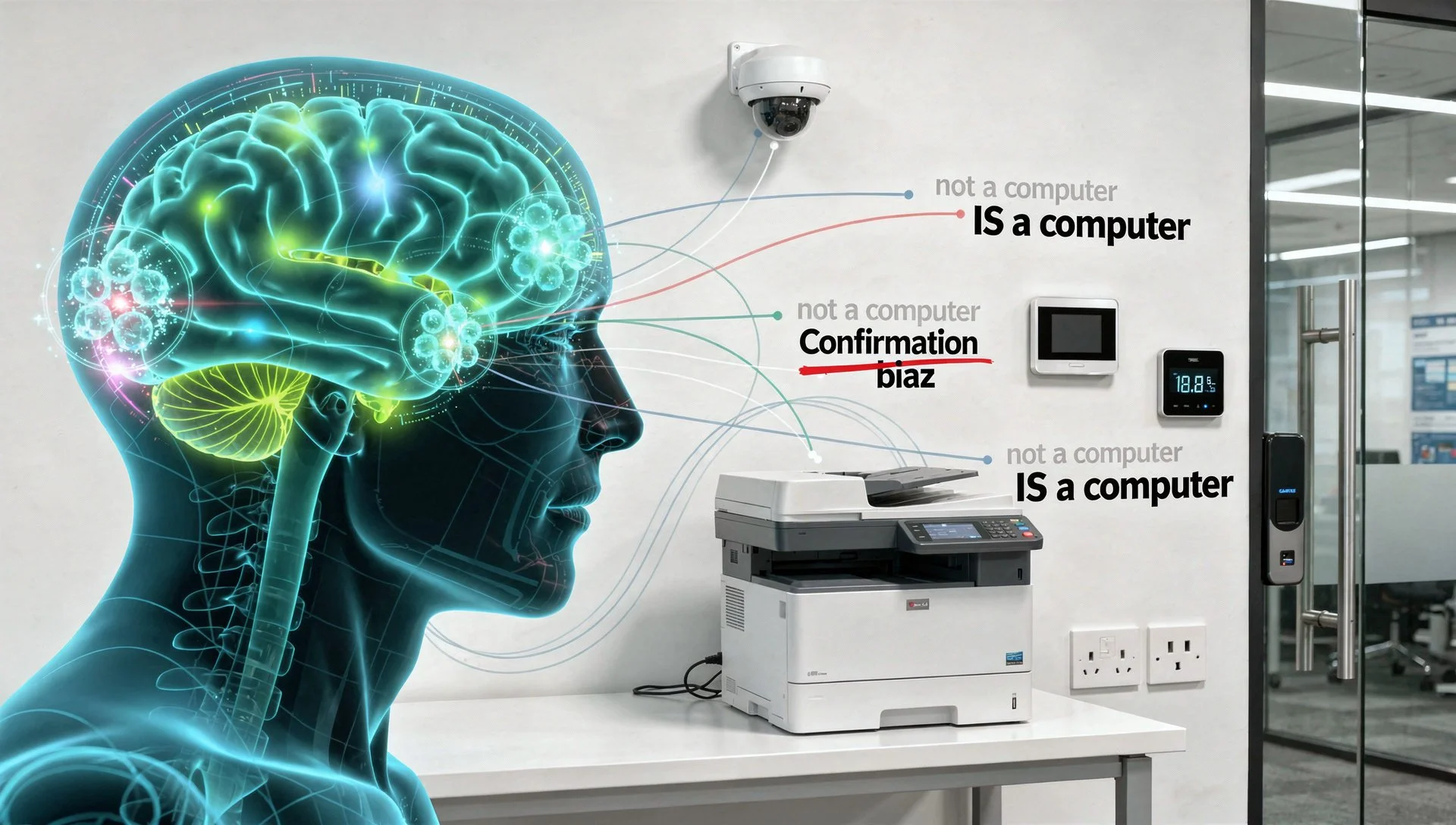
Why Smart People Keep Ignoring Smart Device Security: The Psychology Behind IoT Blindness
After this week's podcast revelation about the marketing agency losing client files through an unsecured printer, my inbox has been full of variations on the same question: how do intelligent business owners with otherwise solid security miss something this obvious?
The answer isn't comfortable, but it's important: IoT security failures aren't about lack of intelligence. They're about systematic psychological blind spots that affect everyone from small business owners to government departments.
Former UK Government analyst reveals the cognitive biases costing UK businesses millions and, more importantly, how to overcome them before your next security decision. Understanding the psychology prevents the breach.
Your £15,000 Security Investment Just Got Defeated by a £300 Printer
Right, let's talk about the £15,000 security investment that just got absolutely destroyed by a £300 office printer. A marketing agency did everything right: new firewalls, endpoint protection, hardware authentication keys for every staff member, security audit came back clean. Two months later? Someone had been accessing their client files for weeks through their HP printer still using admin/admin as credentials. While you've been securing laptops and servers, your printer has full network access, stores every document you print, and still uses the password it shipped with. Pull up a chair, this intervention is long overdue.
The Devices You Forgot Were Computers - IoT Security for Small Business
What if I told you the biggest cyber threat to your business isn't hackers, but your office printer? Sounds mad, right? That's what a 30-person marketing agency thought before someone accessed their client files for weeks through an HP printer with factory default credentials. Episode 30 reveals the devices everyone forgets are computers: printers storing documents, CCTV systems livestreaming your premises, thermostats providing network access. Currently Top 12 in Apple Podcasts Management category worldwide with 3,500 daily downloads. Thirty episodes making cybersecurity almost entertaining whilst being brutally honest. Listen now. Check your printer later. You'll understand why.
The Complete SMB Toolkit for Reverse Benchmarking: Free and Budget Tools That Actually Work
Right, enough theory. Today we're getting practical: the actual tools, templates, and processes you need to implement reverse benchmarking without spending a fortune. Everything in this guide is either free or costs less than a decent takeaway curry per month. Because I'm sick of "enterprise security" guides that assume unlimited budgets and dedicated staff. This is the real-world, shoestring-budget, one-person-wearing-multiple-hats implementation guide. Asset inventory using Google Sheets: free. Vulnerability scanning with OpenVAS: free. MFA with authenticator apps: free. Security advisories via email: free. The British Library spent £7 million recovering from ransomware. Prevention would have cost £10,000-20,000 annually. Budget isn't your excuse anymore.
The Psychology of Security Failures: Why Smart People Keep Making the Same Stupid Mistakes
Noel spent Monday and Tuesday explaining what reverse benchmarking is and how to implement it technically. Both excellent.
Both necessary. Both completely inadequate if you don't understand why organizations systematically fail to learn from disasters. Here's the uncomfortable truth: most breaches happen not because organisations don't know what to do, but because human psychology actively prevents them from doing it.
Normalcy bias makes us believe disasters happen to others. Optimism bias creates illusions of control. Blame cultures suppress incident reporting. The fundamental attribution error prevents learning from failures. Your brain evolved for different threats in different environments. The cognitive biases that kept us alive now get us breached.
When Security Royalty Gets It Dangerously Wrong: Debunking the "Stop Hacklore" Letter
86 security professionals including former CISA director published advice last year claiming public WiFi, QR codes, and USB charging stations are safe.
Sounds credible, except I've spent the year mopping up after businesses who followed exactly this advice. £47,000 stolen via hotel WiFi. Companies breached via QR code phishing. Legal practice ransomwared through compromised charging station.
When security elite operate in enterprise bubbles with unlimited budgets, their advice becomes dangerous for SMBs without those luxuries.
Here's the evidence-based reality, complete with actual incident costs and why defence in depth isn't folklore.
Reverse Benchmarking: Why Studying Cyber Failures Beats Copying Best Practices
Most people copy what the big players do and call it a cyber strategy. That works for them. It probably kills you. This episode flips the script. Instead of worshipping best practice, we dissect the car crashes.
Target, Equifax, Colonial Pipeline and SolarWinds. We ask one question. What actually went wrong and have you quietly made the same mistakes in your own business.
If you run a UK small or mid sized firm and feel lost in security buzzwords, this is your shortcut. Learn from other peoples disasters before you become the next case study. Your future self will approve.
⚠️ Full Disclaimer
This is my personal blog. The views, opinions, and content shared here are mine and mine alone. They do not reflect or represent the views, beliefs, or policies of:
My employer
Any current or past clients, suppliers, or partners
Any other organisation I’m affiliated with in any capacity
Nothing here should be taken as formal advice — legal, technical, financial, or otherwise. If you’re making decisions for your business, always seek professional advice tailored to your situation.
Where I mention products, services, or companies, that’s based purely on my own experience and opinions — I’m not being paid to promote anything. If that ever changes, I’ll make it clear.
In short: This is my personal space to share my personal views. No one else is responsible for what’s written here — so if you have a problem with something, take it up with me, not my employer.